Application Access Request
Application Access Request
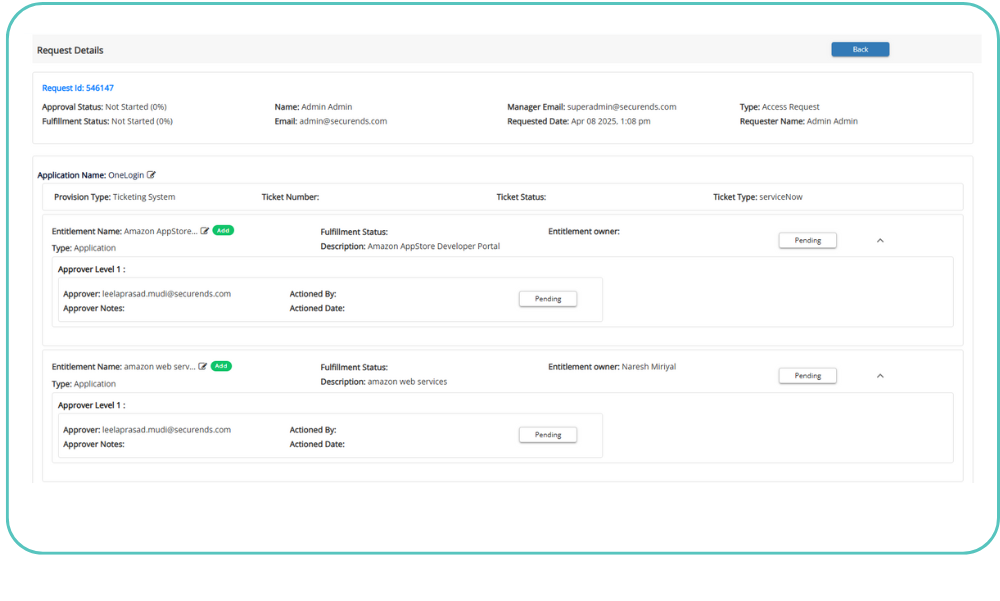
SecurEnds application access request extends birthright provisioning to deliver access request capability for users needing additional access by automating self-request and approval workflow
Every user in an organization goes through a Joiners, Movers, and Leavers (JML) lifecycle. This process kicks off with the addition of a new user in the company’s system of record (Human Resources system for an employee or Microsoft Azure AD for a contractor). This birthright provisioning provides uses access to basic applications and data based on their role. Many times, users need access to additional applications or data outside of their birthright access. Having a non-centralized process makes it difficult for requesters to get access in a timely fashion. Other times highly regulated companies require line manager or application owner approvals before access is provisioned for critical applications.
SecurEnds Application Access Request is a centralized access request management solution that simplifies the access request and approval process helping companies adhere to the principle of least privileged access. Access Request allows users and their managers to request access to IT assets and for their managers to review and approve the requests. The combined offering of SecurEnds Identity Lifecycle Management (ILM) and Access Request allows productivity and auditability for all requests and access control.
With SecurEnds simple, intuitive shopping cart and inbuild multi-level approval workflow, managers, security analyst and application owners can automate access requests for:
Privileged Users
Minimize the footprint of admin accounts and ensure every account is created using the principle of least privileges.
Third Party Users
Third-party vendors change often and typically only need access for a brief period of time. Documenting what and why of their access allows your company to reduce risk and monitor what outsiders can access. Approvers may also select a time limit for the access and receive notifications when the access should be removed.
Avoid Segregation of Duty Conflicts
Using the multi-level approval workflow, Segregation of Duty conflicts can be prevented before the violations occur. This reduces audit findings and allows for documented evidence to be reported on.
Service Account Governance
Without a defined repeatable process in place service accounts tend to be created in an ad-hoc manner and given the keys to the kingdom. Introducing an access request process increases visibility and requires users to present a business case for the request being made.
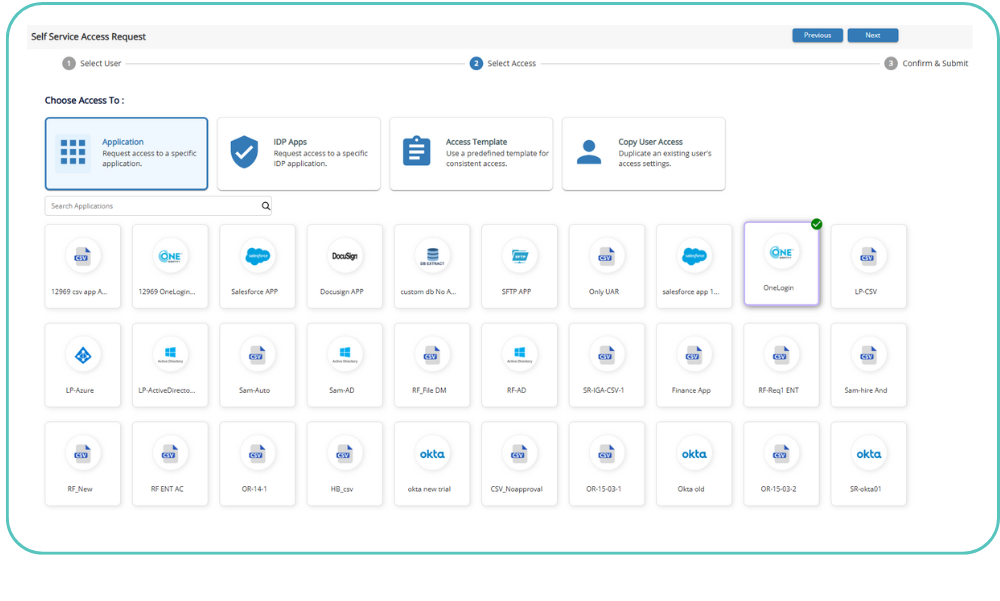
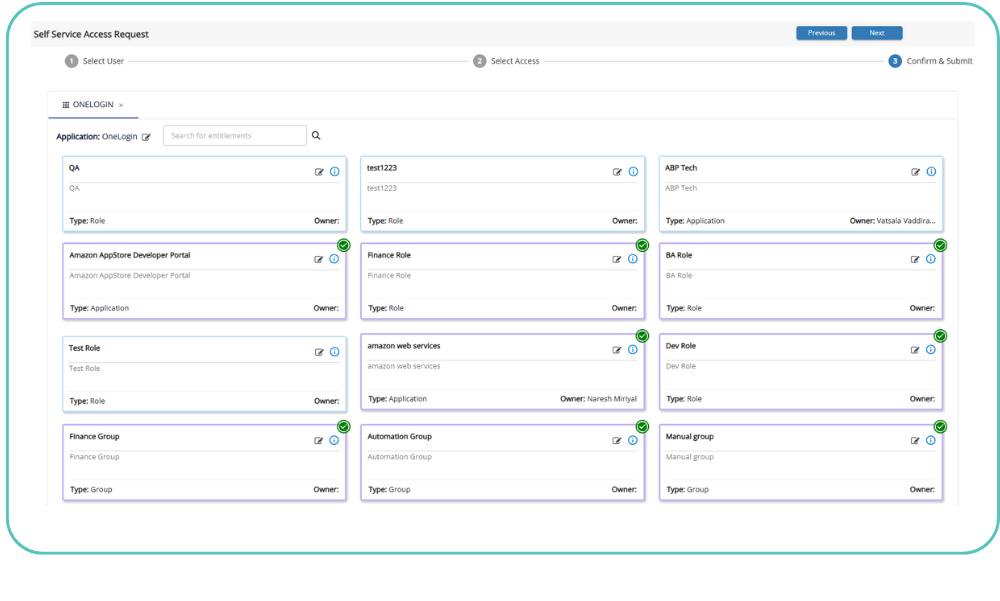
Application Groups
In SecurEnds Application Access Request roles and groups are sets of applications and permissions within those applications. Users may have multiple groups assigned to them. This separates the concept of an HR position from what is needed to get the job accomplished. Managers may also request applications not needed by others in the role for special projects or unique skillsets.
The Right Access. To the Right People. At the Right Time.
Features
The key benefits of SecurEnds Application Access Request
Manage risk across different user types
In light of the recent breaches third-party access is the greatest point of risk. As third-party users are not in HR system and hence cannot be automatically deprovisioned with ease extra care is required in provisioning these accounts. SecurEnds allows the right users the right access at the right time by having line managers approve Joiner, Mover, Leaver events.
Achieve regulatory compliance
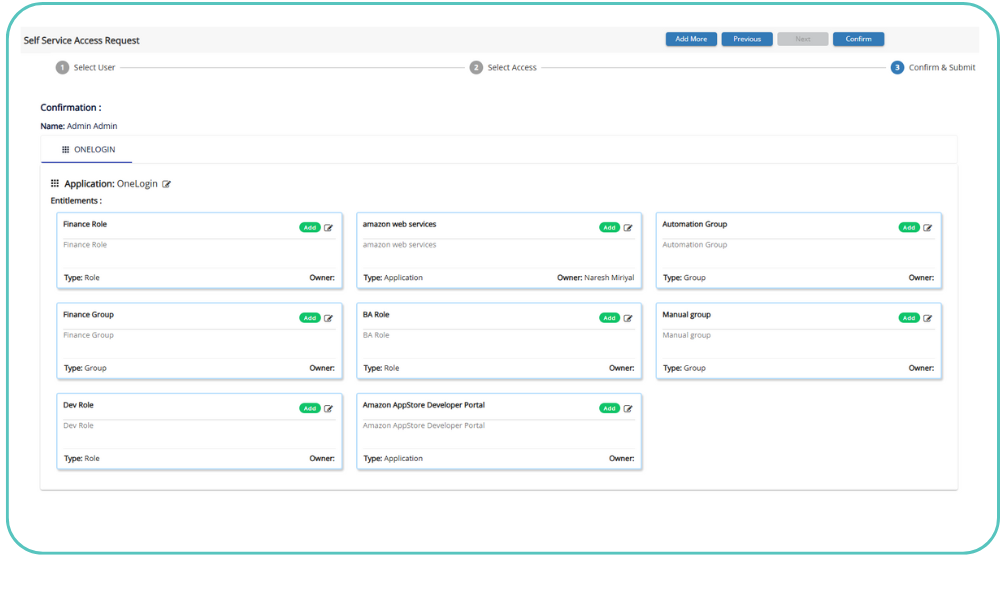
Every user provisioning request and approval workflow is logged in SecurEnds. This enables internal security organizations to create proof of compliance during the annual audits.
Demonstrate Access Controls
A customized access approval workflow that allows different types of access controls– no approval, single approver, single level with multiple approvers, multiple levels of approvals with each level having multiple approvers
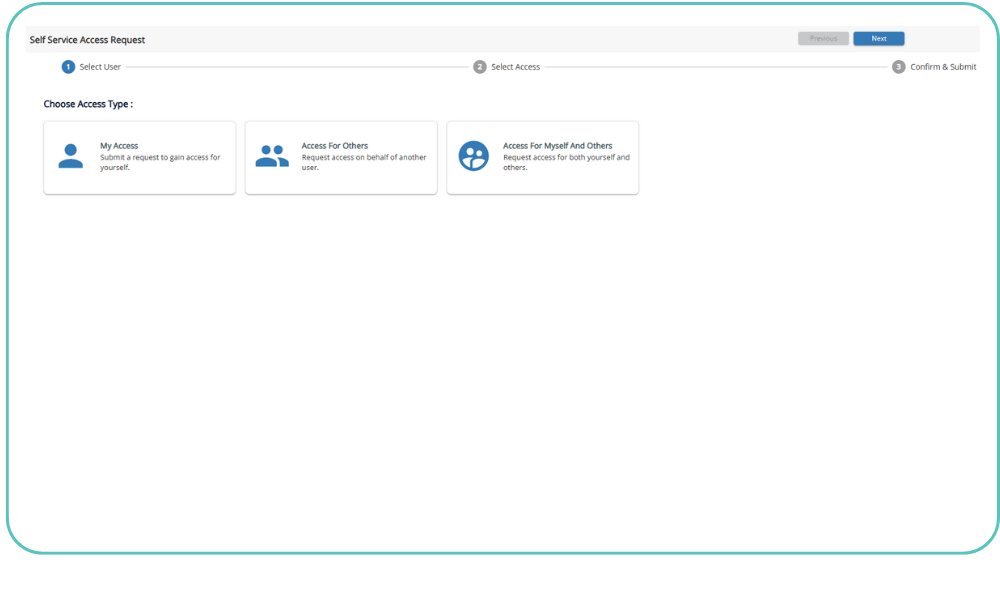
End users can self-serve
The end user does not need to know technical jargon or follow IT processes to request access. SecurEnds Access Request uses shopping cart experience to guide the user through the access request process.